Risk-based ECM decision making
In a previous post, we looked at ways to use process analysis to inform ECM decision making. In this post, we’ll look at one way to use a risk analysis to do the same.
A basic risk analysis exercise has four steps:
- List risks
- List mitigations
- Categorize mitigations
- Rank mitigations
Depending on the complexity of the organization and the level of stakeholder involvement required, this exercise could be as simple as a single, 90-minute facilitated workshop or as complex as a multi-session effort lasting a few weeks (or months). Regardless of the size of the effort, the core activities you’ll need to perform are the same.
1. List risks
This is run as a typical brainstorming session, the goal being to gather as many risks from the participants as possible without editorializing, editing, censoring, providing feedback or commentary, etc. It can be helpful when facilitating to think about the big bucket categories of risk at your organization and begin with those on the board both to get the conversation going and to guide it in a productive direction from the very start.
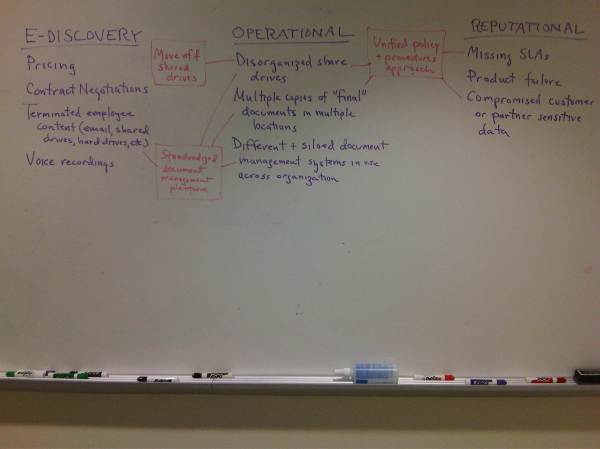
Although there are lots of ways to use the whiteboard to facilitate a risk brainstorming session, I suggest leaving space between the big bucket categories you’ve written on the board so that in step two, you can write the relevant mitigations adjacent to the risks they address. The picture below shows an example of what a typical whiteboard might look like after a risk brainstorming session.

Throughout, don’t get too hung up on figuring out exactly what bucket a risk goes into—take your best guess (or accept the best guess of the room) and move on. It’s more important to get the ideas flowing than to categorize with 100% accuracy…you can always go back and do that after the session.
2. List mitigations
Listing mitigations is also run as a brainstorming session, but rather than beginning from big bucket categories of mitigations, it’s most helpful to begin with the gathered list of risks itself. Often this begins organically during the process of listing risks, as folks spontaneously offer ideas on how to address the risks up on the board. When this happens, it’s important not to discourage them or to insist on a hard and fast division between listing risks and listing mitigations. Instead, keep a “parking lot” list of mitigations and let the flow of ideas continue with limited interruption.
No matter how you transition to listing mitigations, the key activity is to tie each mitigation to the risk or risks it addresses. I normally do this by switching pen colors on the whiteboard and using the space I’ve left between the risk type columns: write the mitigation near the risk or risks it best addresses and then connect it with an arrow to the relevant risks. However, you can accomplish this in whatever way works best for you, fits your facilitation style, etc. The picture below is an example of what a typical whiteboard might look like after the kind of mitigation brainstorming session I’ve described here.
3. Categorize mitigations
Once you’ve gone through the process of gathering all the risks and their associated mitigations, you need to categorize the mitigations along meaningful dimensions. For driving ECM decision making, the relevant dimensions I use in my practice are the following:
- Change behavior – will the mitigation require people to do things differently?
- Buy technology – will the mitigation require new technology to be purchased?
- Hire resources – will the mitigation require new hires?
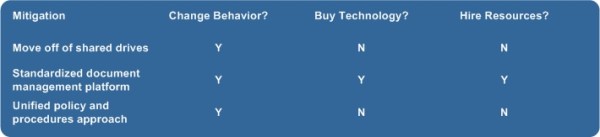
The easiest way to do this is with a matrix, such as the following.
I’ve made this example fairly simple to get the basic concepts across. But in your practice, you’ll likely have many more categories, some of which will be very specific to the enterprise. For example, if the CIO has published a list of key IT initiatives for the year, you might have a column called “CIO Initiative” and place the name of the initiative that a given mitigation relates to, piggy backs on, or contributes to; or if there is a piece of key legislation or regulation that governs the organization’s work , you might have a column called “Regulation Such-and-such” and put a “Y” for any mitigation that helps the organization comply with it. Basically, the idea is that you should have a column for each criteria that will impact the decision to go ahead with risk mitigation or not or will materially affect the decision-making about how to manage risk.
4. Rank Mitigations
With all the mitigations listed and categorized, the final step is to rank them. Although you can get pretty fancy with how you do this, the easiest way is to move from left to right through the categories on the matrix above, because the mitigations get increasingly “expensive” to the organization as you do.
So, any mitigations that require only a change in behavior with no tech spend or new hires are ranked first, as they will be the least “expensive” to implement—note that I didn’t say “easiest”, because changing user behavior is just as (if not more) difficult to do successfully than buying technology. Next come those that only require technology spend, followed by those that require hiring resources; then come those that require tech spend and behavior change, followed by those that require new hire and behavior change; and finally come those that require all three.
The final word
At this point, you have the raw materials you need to begin working out a risk management plan with your stakeholders—that is, detailing what risks they face, what mitigations are available, what it will “cost” to implement each, and which they have decided to implement and which not (and why).
In the end, there are lots of ways to approach risk management using exercises like this one. I’d love to hear from folks who have other ways to get stakeholders to work through risk management using this method or any others.